stringjunior
A Stringer original
A matter of high priority indeed. Good skills Highbury_Blade
Is a new CB also a high priority? That's not a dig btw...
Is a new CB also a high priority? That's not a dig btw...
Follow along with the video below to see how to install our site as a web app on your home screen.
Note: This feature may not be available in some browsers.
All advertisments are hidden for logged in members, why not log in/register?
Also incidentally, the guy that runs that Site - Troy Hunt - is reasonably popular in the online security world. I am tempted to contact him if the club doesn't sort this out.
Hi, only just seen this thread and it got my attention! Can I ask is this just about the insecure storage of passwords for the site (bad enough in itself) or is it also about insecure storing of card details? Apologies if you already said but I have tried looking back thru all the posts and didn't see anything. I have sometimes had my worries when using the online ticketing system- the site does seem to play up sometimes. Think the talent.co.uk bit that they link to for the ticketing is used by all the football league clubs isn't it? Cheers, some great detective work there on your part HB!
It's passwords. But given that the security isn't great on them, who knows what else they could be doing? As far as i know, they don't store card details.
The provider they use is used by a number of football leagues and premier clubs, but not all of them have this vulnerability.
I just logged on ok so the site is up. Might be worth emailing them, I once had a problem logging on and they responded to an email and fixed it quite quickly.Can't log on at the moment. If I can't get a ticket today, I won't bother tomorrow when the price goes up.
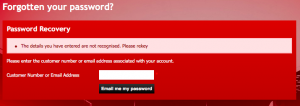
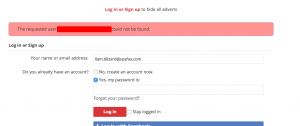
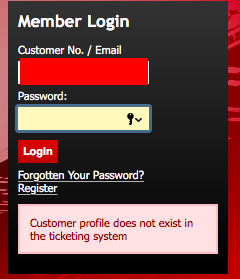
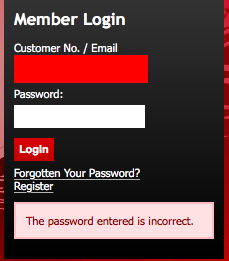
Fucking hell, just found another couple of vulnerabilities, both enabling the same Email Enumeration attack.
View attachment 14157 View attachment 14158
A login form should simply say Details are invalid whenever an incorrect password/username is entered. It should NEVER divulge any information as to whether it was the password or the username that was incorrect.
As i say, if an attacker has a big list of emails then all they have to do is spam the website looking for responses as to whether the email address exists or not. Once they've got a valid email address then they can then spam the website attempting to login using a list of commonly used passwords which no doubt some people will use.
They don't even need a list of email addresses, given that you can log in with a customer number which is just an integer.
That could be stopped if the website rate limited logins, but given the lax security elsewhere i'm guessing they don't.
Also. the requirements for password protection are laughable. Only 4 characters, no mixed casing, no non-alpahnumeric characters.
This isn't Sheffield United's software, it's provided by a third party, but I've raised this multiple times with the club, so it is their fault for not following it up.
Maybe i'll have a word with someone tonight
The website is a template used by most clubs.
Basically it's been contracted out to cowboys.
I imagine you're not getting a response bc literally no-one knows what you're talking about. This isn't a criticism of anyone, just a fact of ICT life.
You'd need to get through to someone in a high level position capable of understanding the issues involved and doing something about it.
But given that we're handing over control of nuclear power plants to the Chinese maybe there's no-one in the country with both the authority and the understanding to address this issue. Given what Stuxnet did isn't this, eventually, national and cultural suicide? Or not?
Pull the other one. I work in IT, these people are as rare as rocking horse shit.someone in a high level position capable of understanding the issues involved
Excellent work Highbury. I don't usually post outside general blades chat, but this is something I've both had trouble with in the past and also understand, as you do. As far as security systems go, on a seperate interface from the original site, it is incredibly easy for a hacker to gain access in any which way they fancied.The ticketing system is a separate system from the website itself.
Phipps did get back to me on Facebook, but heard nothing since.
Everton are using the same system as us and they're vulnerable too. Liverpool use the same company but a different system which doesn't have the same vulnerabilities.
I've just realised this is in general blades chat, woops not sure why I thought otherwise.barnyblade i'm drinking at the moment, but I'll pm you tomorrow. Need to get as much evidence together as possible to take this to the club and shame them into putting funds into getting the system upgraded.
The club could afford it but instead choose to to spend money on reserve players wages instead.
I've just realised this is in general blades chat, woops not sure why I thought otherwise.
How do you plan on taking this to the club out of interest? I seem to remember Phipps acknowledging the problem on facebook a while ago, swiftly followed by zero attempt to sort it. Was it you that raised it with him? Can't remember now.
Yeah that was me. I'm at the dinner thing tonight. I might mention when I'm completely mullered
Maybe i'll have a word with someone tonight
I don't think anyone will be in attendance that will be able to do anything/in a position to understand. Will bring it up again with the relevant people myself this week.
Other steps are in place here to alleviate such an issue as described above.
I'm only winding you up
I know
You lot not out pre-evening in the Plat?
We're down kelham island at the moment then meeting in the copthorne at 7
sort of on a par with how a major ISP operates then - Talktalk say they don't even know what customer details are encrypted and what aren't.Not just us.
]
sort of on a par with how a major ISP operates then - Talktalk say they don't even know what customer details are encrypted and what aren't.
I know. I suspect they have found customer info stored, possibly unencrypted, on the actual web server in the DMZ, where it should not have been stored, because they said the back end systems were not accessed.There's absolutely no way they don't know. It's not like it's a magical thing that sorts itself.
All advertisments are hidden for logged in members, why not log in/register?
